
Juniper Networks vSRX Virtual Firewall
Security professionals to deploy and scale firewall protection in highly dynamic environments

More pricing below,
click here!
Please Note: All Prices are Inclusive of GST
Overview:
Data centers increasingly rely on server virtualization to deliver services faster and more efficiently than ever before. The virtualized data center, however, introduces new challenges that require additional security considerations beyond those needed to secure physical assets.
Virtual machines (VM) can be highly dynamic and elastic in a virtualized data center, with frequent additions, moves, and changes. These frequent changes complicate the ability to attach security policies to a VM instantiation and track security policies with VM movement to ensure continued regulatory compliance. In short, the dynamic and flexible nature of virtualization can easily lead to a loss of visibility and control.
Network and security professionals must perform a delicate balancing act, delivering the benefits of virtualization and cloud technologies without undermining the organization's security. This challenge can only be met by a security solution that can keep pace with evolving threats while matching the agility and scalability of virtualized and cloud environments-without sacrificing reliability, visibility, and control.
Juniper addresses these challenges head-on by extending the capabilities of the award winning Juniper Networks® SRX Series Services Gateways to the virtual world with the vSRX Virtual Firewall. Juniper makes security easy by securing the cloud at every level: between applications, between instances, and across environments.
Powered by Juniper Networks Junos® operating system, the vSRX delivers a complete and integrated virtual security solution, including L4-L7 advanced security services, robust networking, and automated life cycle management capabilities for service providers and enterprises alike.
The vSRX's automated provisioning capabilities allow network and security administrators to quickly and efficiently provision and scale firewall protection to meet the dynamic needs of virtualized and cloud environments. By combining the vSRX with the power of Junos Space® Security Director, administrators can significantly improve policy configuration, management, and visibility into both physical and virtual assets from a standard, centralized platform.
For service providers and organizations deploying service-oriented applications in software, the vSRX's portfolio of virtualized network and security services supports a variety of Network Functions Virtualization (NFV) use cases. The vSRX also supports Juniper Networks Contrail, OpenContrail, and other third-party solutions, and can be integrated with other next-generation cloud orchestration tools such as OpenStack, either directly or through rich APIs.
Product Overview
The vSRX Virtual Firewall delivers a complete virtual firewall solution, including advanced security, robust networking, and automated virtual machine life cycle management capabilities for service providers and enterprises. vSRX empowers security professionals to deploy and scale firewall protection in highly dynamic environments.
Architecture and Key Components:
Advanced Security Services
Implementing nonintegrated, legacy systems built around traditional firewalls and individual standalone appliances and software is no longer adequate to protect against today's sophisticated attacks. Juniper's advanced security suite enables users to deploy multiple technologies to meet the unique and evolving needs of modern organizations and the continually changing threat landscape. Realtime updates ensure that the technologies, policies, and other security measures are always current.
The vSRX delivers a versatile and powerful set of advanced security services, including content security, intrusion detection and prevention (IDP/IPS), and application control and visibility services through Juniper Networks AppSecure.
Content Security
The vSRX includes comprehensive content security against malware, viruses, phishing attacks, intrusions, spam, and other threats with best-in-class antivirus, antispam, Web filtering, and content filtering features.
| Features | Feature Description | Benefits |
|---|---|---|
| Antivirus | Reputation-enhanced, cloud-based antivirus capabilities that detect and block spyware, adware, viruses, keyloggers, and other malware over POP3, HTTP, SMTP, and FTP protocols Service provided either on-box or in the cloud |
Sophisticated protection from respected antivirus experts against malware attacks that can lead to costly data breaches and lost productivity |
| Web Filtering | Enhanced Web filtering, including extensive category options (90+ categories) and a real-time scorecard | Protection against lost productivity and the impact of malicious URLs, as well as helping to maintain network bandwidth for essential business traffic |
| Content Filtering | Effective inbound and outbound content filtering based on MIME type, file extension, and protocol commands | Protection against inadvertent or malicious file transmitting and malicious content on the network to minimize the risk of compromise or data leakage |
| Antispam | Multilayered spam protection, up-to-date phishing URL detection, standards-based S/MIME, Open PGP and TLS encryption, MIME type, and extension blockers |
Protection against advanced persistent threats perpetrated through social networking attacks and the latest phishing scams with sophisticated e-mail filtering and content blockers |
Intrusion Prevention System (IPS)
IPS for vSRX controls access to IT networks to protect systems from attack by inspecting data and taking actions such as blocking attacks as they are developing-and before they succeed-or creating a series of rules in the firewall. IPS tightly integrates Juniper's applications security features with the network infrastructure to further mitigate threats and protect against a wide range of attacks and vulnerabilities.
| Features | Feature Description | Benefits |
|---|---|---|
| Stateful signature inspection | Signatures are applied only to relevant portions of the network traffic determined by the appropriate protocol context. | Minimizes false positives and offers flexible signature development. |
| Protocol decodes | More than 65 protocol decodes are supported, along with more than 500 contexts to ensure proper protocol usage. | Improves signature accuracy through the precise context of protocols. |
| Signatures | There are more than 15,000 signatures for identifying anomalies, attacks, spyware, and applications. | Attacks are accurately identified and attempts to exploit known vulnerabilities are detected. |
| Traffic normalization | Reassembly, normalization, and protocol decoding provided. | System overcomes attempts to bypass other IPS detections by using obfuscation methods. |
| Zero-day protection | Protocol anomaly detection and same day coverage for newly found vulnerabilities provided. | Protects networks against any new exploits. |
| Recommended policy | The Juniper Security Team identifies attack signatures as critical for the typical enterprise. | Installation and maintenance are simplified while ensuring the highest network security. |
| Active/active traffic monitoring | IPS monitoring includes active/active vSRX chassis clusters. | Support included for active/active IPS monitoring. |
| Packet capture | IPS policy supports packet capture logging per rule. | Users can conduct further analysis of surrounding traffic and determine additional steps to protect the target. |
Application Visibility and Control with AppSecure
AppSecure is a next-generation application security suite for vSRX and SRX Series Services Gateways that delivers threat visibility, protection, enforcement, and control.
Whether needing to understand how many users are accessing cloud-based applications like Facebook every day, or needing to know what applications are using the most bandwidth, AppSecure delivers powerful visibility and ongoing application tracking. With open signatures, unique application sets can be monitored, measured, and controlled to tie closely to the organization's business priorities.
| Features | Feature Description | Benefits |
|---|---|---|
| AppTrack | Analyzes application data and classifies it based on risk level, zones, source, and destination addresses. | Tracks application usage to identify high-risk applications and analyze traffic patterns, improving network management and control. |
| AppFW | Creates application control policies to allow or deny traffic based on dynamic application or group names. | Enhances security policy creation and enforcement based on applications rather than traditional port and protocol analysis. |
| AppQoS | Meters and marks traffic based on the application security policies set by the administrator. | Prioritizes traffic and limits and shapes bandwidth based on application information and context to improve overall performance. |
Juniper Advanced Threat Prevention
Juniper Advanced Threat Prevention integrates with the vSRX to provide dynamic, automated protection against known malware and advanced zero-day threats, resulting in instantaneous responses
Security policies determine if a session can originate in one zone and be forwarded to another zone. The vSRX receives packets and keeps track of every session, every application, and every user. As a VM moves within a virtualized or cloud environment, it will still send packets to the vSRX for processing, continuously communicating in a secure mode.
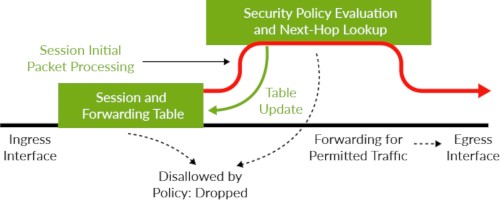
vSRX session-based forwarding algorithm
| Features | Benefits |
|---|---|
| Deep inspection and analysis | Extracts compromised files and sends them to the cloud to rapidly identify known threats or deep-level file analysis that looks for particularly evasive malware. |
| Instant identification to block attacks | Instantly identifies and communicates detected malware to SRX Series firewalls to block attacks. |
| Web-based portal with rich reporting and analytics tools | Provides a web-based interface for performing management tasks such as configuration and product updates. It also offers a rich set of reporting and analytics tools that provide visibility into threats and compromised hosts. |
| Quarantine of systems and hosts | Analytics capability lets administrators and security staff analyze and correlate data, identifying compromised systems and feeding the information to SRX Series firewalls to quarantine those systems. |
| SecIntel | Dynamic threat intelligence feeds offered through SecIntel cascade threat information to SRX Series firewalls for immediate action. |
| Command and control (C&C) data | Provides C&C data to the SRX Series firewalls, preventing compromised internal systems from communicating with these devices. |
| E-mail analysis and remediation | Isolates and quarantines malicious malware, preventing e-mail from being used as an attack vector. Machine learning algorithms analyze e-mail traffic, detect malicious attachments, and block files at the firewall. |
| Threat intelligence | Uses powerful open APIs for seamless integration with third-party vendors, providing multiple threat intelligence feeds and reducing the attack surface. |
| Encrypted Traffic Insights | Restores visibility into traffic lost due to encryption without the heavy burden of full TLS/SSL decryption. |
| Adaptive Threat Profiling | Enables a quicker response time to combat the continuous onslaught of new threats. Organizations can use ATP Cloud’s Adaptive Threat Profiling to automatically create security intelligence threat feeds based on who and what is currently attacking the network. |
High Availability (HA)
The vSRX provides mission-critical reliability, supporting chassis clustering for active/active and active/passive modes. The HA functionality provides full stateful failover for any connections processed and for cluster members to span hypervisors. When configured in a cluster, vSRX VMs synchronize the connection/ session state and flow information with IPsec security associations, Network Address Translation (NAT) traffic, address book information, configuration changes, and more. As a result, not only is the session preserved during failover, but security is also kept intact. In an unstable network, vSRX also mitigates link flapping.
Juniper Secure Connect
Juniper Secure Connect is a highly flexible SSL VPN application that provides secure access to corporate and cloud resources for employees working away from protected resources. Juniper Secure Connect is available for desktop and mobile devices including Windows, Mac OS, Android, and iOS. When combined with the SRX Series Services Gateways, Secure Connect helps organizations achieve dynamic, flexible, and adaptable connectivity to any device anywhere, reducing risk by extending visibility and enforcement from users to cloud.
vSRX Services Gateway Key Performance Metrics
| Performance and Capacity1 | VMware | KVM | ||||||
|---|---|---|---|---|---|---|---|---|
| vCPUs | 2 | 5 | 9 | 17 | 2 | 5 | 9 | 17 |
| Memory | 4 GB | 8 GB | 16 GB | 32/64 GB | 4 GB | 8 GB | 16 GB | 32/64 GB |
| Firewall throughput, large packet (1514B) | 15.7 Gbps | 41 Gbps | 73 Gbps | 81 Gbps | 17 Gbps | 50 Gbps | 79 Gbps | 141 Gbps |
| Firewall throughput, IMIX | 3.2 Gbps | 11.1 Gbps | 17 Gbps | 27 Gbps | 4.3 Gbps | 12.5 Gbps | 22 Gbps | 40 Gbps |
| AES+GCM IPSec VPN throughput (1420B) | 2.1 Gbps | 3.8 Gbps | 12 Gbps | 13 Gbps | 2.9 Gbps | 6.3 Gbps | 10.8 Gbps | 14.9 Gbps |
| Application visibility and control2 | 3.7 Gbps | 10.8 Gbps | 21 Gbps | 39 Gbps | 2.4 Gbps | 10.8 Gbps | 20.7 Gbps | 35.8 Gbps |
| IPS recommended signatures | 3.6 Gbps | 11 Gbps | 18 Gbps | 39 Gbps | 2.2 Gbps | 12.6 Gbps | 20.8 Gbps | 36.2 Gbps |
| TCP connections per second | 55,000 | 166,250 | 351,250 | 537,660 | 69,000 | 239,380 | 360,000 | 612,660 |
| Maximum concurrent sessions3 | 512,000 | 2M | 4M | 12/28M | 512,000 | 2M | 4M | 12/28M |
| Number of remote access/SSL VPN (concurrent) users | 500 | 500 | 500 | 500 | 500 | 500 | 500 | 500 |
1 All performance numbers are "up to" and depend on the underlying hardware configuration (some server configurations may perform better). Performance, capacity and features listed are based on vSRX running Junos OS 20.4R1 release and are measured under ideal testing conditions. Actual results may vary based on Junos OS releases and by deployments
3 Throughput numbers based on HTTP traffic with 44KB transaction size.
3 Maximum concurrent sessions can be increased based on the memory allocation for the vSRX. For more information, visit https://www.juniper.net/documentation/en_US/vsrx/information-products/topic-collections/release-notes/19.2/topic-98044.html#jd0e119
Performance
Traditionally, customers must choose between scalability and performance. The vSRX solution is optimized to leverage multiple virtual CPUs to maximize packet processing and overall throughput in the virtual environment. Each vSRX VM also has multiple virtual network interface cards (vNICs), which can be connected to various virtual networks to simultaneously protect multiple network segments. The vSRX operates from within the virtual fabric, providing the best of both worlds-strong security with the performance needed to support a virtualized or cloud-based environment.
Leveraging the Software Receive Side Scaling implementation, the vSRX provides additional cores* beyond the minimum two vCPU, up to a maximum of 32 vCPUs, to the same instance without having to certify a new instance image. By using 17 vCPUs from a single socket, the vSRX can achieve up to 98 Gbps performance.
| Virtual CPU Cores | Memory (GB) | Supported NIC Types |
|---|---|---|
| 2 | 4, 8, 16, 20, 32 | VMXNET3, VIRTIO, 82599 SR-IOV, I40E SR-IOV |
| 5 | 8, 16, 20, 32 . | VMXNET3, VIRTIO, 82599 SR-IOV, I40E SR-IOV |
| 9 | 16, 32, 50, 64 | I40E SR-IOV |
| 17 | 32, 50, 64 | I40E SR-IOV |
| 32 | 64 | I40E SR-IOV |
Junos Space Security Director
Junos Space Security Director provides security policy management through an intuitive and centralized web-based interface that offers enforcement across emerging and traditional risk vectors. As an application on the Junos Space platform, Security Director provides extensive security scale, granular policy control, and policy breadth across the network. It helps administrators quickly manage all phases of security policy life cycle for stateful firewall, content security, IPS, AppFW, VPN, and NAT.
Unified Management
Leveraging the power of Junos Space Security Director, administrators can significantly improve policy configuration, management, and visibility into both physical and virtual assets from one common, centralized platform.
Features & Benefits:
- Secures multitenant private and public cloud environments by delivering a complete firewall with stateful packet processing and application-layer gateway features in a virtual machine format
- Leverages the same, consistent, advanced security and networking features (IPsec VPN, NAT, QoS, and full routing capabilities) of the SRX Series Services Gateways
- Defends against an increasingly sophisticated threat landscape by integrating robust content security, IPS, and application visibility and control capabilities for a comprehensive threat management framework
- Improves management flexibility with open RESTful APIs to support integration with third-party management and cloud orchestration tools
- Expands visibility into and control over firewall security policy configuration and management across virtual and non-virtual environments with Junos Space Security Director
- Supports SDN and NFV via integration with Contrail, OpenContrail, and other third-party solutions
Specifications:
| Protocols | IP Address Management | Security | SLA, Measurement, and Monitoring | Hypervisors |
|---|---|---|---|---|
|
|
|
|
|
*Hypervisor support is regularly updated.
Documentation:
Download the Juniper Networks vSRX Virtual Firewall Datasheet (PDF).
Pricing Notes:
- All Prices are Inclusive of GST
- Pricing and product availability subject to change without notice.

