
Juniper Networks Junos Space Security Director
Junos Space Network Management

Our Price: Request a Quote
Our Price: Request a Quote
Our Price: Request a Quote
Click here to jump to more pricing!
Please Note: All Prices are Inclusive of GST
Overview:
In today's complex environment, network security management can become overly time consuming and prone to error if management solutions are slow, unintuitive, or restricted in their level of granularity, control, and visibility. Junos Space Security Director provides security policy management for all physical, logical, and virtual firewalls (SRX Series Services Gateways and vSRX) through an intuitive, centralized, web-based interface that offers enforcement across emerging and traditional risk vectors.
With the addition of Policy Enforcer, Security Director automatically updates policies based on threats identified by Sky Advanced Threat Prevention malware detection in the cloud, as well as those found by onpremises threat intelligence solutions. Updated policies are then distributed to enforcement points such as firewalls and switches, ensuring up-to-theminute network protection.
Juniper Networks Junos Space Security Director, an application that runs on the innovative, intuitive, and intelligent Junos Space Network Management Platform, provides detailed visibility into application performance, reducing risk while enabling users to move quickly from “knowing” something is wrong to “doing” something to fix the problem.
Providing extensive scale, granular policy control, and policy breadth across the network, Security Director helps administrators manage all phases of the security policy life cycle for stateful firewall, unified threat management (UTM), intrusion prevention, application firewall (AppFW), VPN, and Network Address Translation (NAT) through a centralized web-based interface. Security Director reduces management costs and errors by providing actionable intelligence, automation, efficient security policy, intuitive workflows, and a powerful application and platform architecture, allowing users to detect threats as they happen and apply remedial actions in real time.
Policy Enforcer simplifies and automates the process of deploying up-to-the-minute enforcement. An intuitive user interface gives administrators the flexibility to selectively control and modify network elements, enforcement groups, threat management services, and profile definitions.
The Security Director dashboard provides customizable, information-rich widgets offering visually intuitive displays that report security device status at a glance. A pallet allows you to easily navigate between firewall, threat, intrusion prevention system (IPS), application, throughput and device-related information, which can be used to create a customized view of the Juniper Networks SRX Series Services Gateways firewall environment. Through the dashboard, you can quickly determine which SRX Series devices have the most alarms, or which have consumed the most CPU cycles or RAM for a specific time period. A Threat Map widget shows the number of IPS events detected per geographic location, giving you industry-leading information gathering and remediation capabilities.
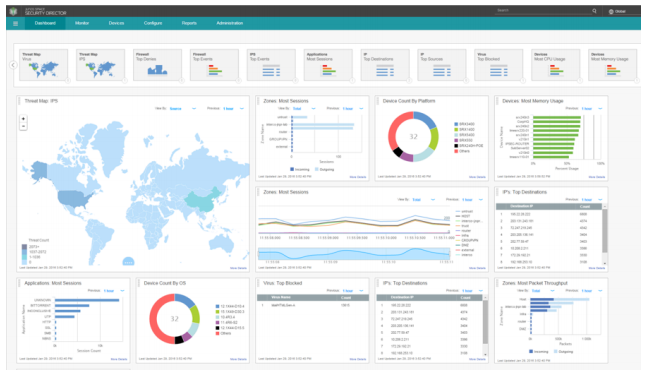
Figure 1: Junos Space Security Director dashboard
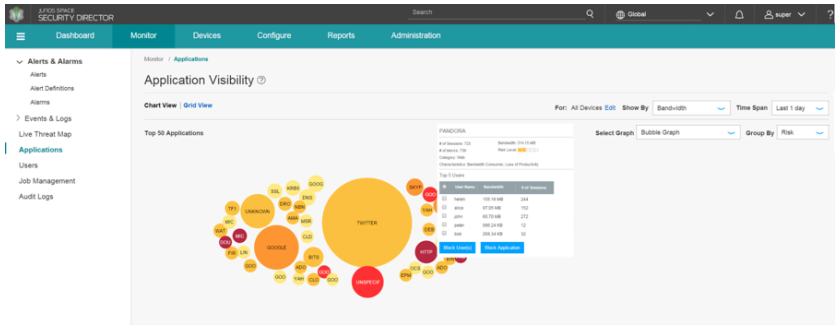
Figure 2: Application Visibility dashboard feature
Drilling down on widgets, users can sort and search various events to effortlessly obtain detailed information such as top viruses blocked, top destinations, top sources, and other details that can be used to ensure that the network is safe.
Security Director offers the industry's most innovative solution for managing the application, user, and IP environment. Network administrators can choose between three different views to see how applications and users are affecting the network, observe bandwidth utilization levels, or determine the number of sessions created. Granular usage details, such as which applications are the riskiest, can be viewed. Top talkers are easy to identify and remediate. Different time frames can also be compared to determine when utilization is typically at its peak.
Unlike other products, Security Director does not require users to run multiple reports or open multiple tabs and then manually analyze the data to determine who is using which applications and to what extent. Instead, Security Director allows administrators to easily correlate users to applications by simply selecting an application icon or a user/user group icon.
Blocking traffic from a specific country is also easy and intuitive. Using Security Director's Live Threat Map, it's not only possible to see where threats are originating, you can also block traffic coming from or going to a selected geographic location.
Actionable Intelligence
With most security management solutions, administrators have to run a report or open several tabs to find the applications or users they want to manage. Then they must manually create the required firewall rules, determine where to place those rules, and hope they don't conflict with any existing rules, thereby creating a host of new problems. This is a tedious, time-consuming, and error-prone process.
Security Director offers an Actionable Intelligence feature that eliminates the need to engage in this antiquated exercise. Using Actionable Intelligence, administrators can select one or more applications or user/user groups from the Application Visibility or User Visibility charts, then simply select “Block.” Security Director automatically creates the requested rule or rules and deploys them in the optimal location within the rules base, avoiding any anomalies and taking the guesswork out of managing the application and user environment.
Features and Benefits:
| Features | Feature Description | Benefits |
|---|---|---|
| Policy Enforcer | Creates and centrally manages security policies through a user intent-based system, evaluating threat intelligence from multiple sources while dynamically enforcing policies in near real time across the network. Enforces threat management policies at firewalls and access switches, aggregating threat feeds from Sky Advanced Threat Prevention, Spotlight Secure, and on-premises custom threat intelligence solutions with white and black list support. |
|
| Firewall policy analysis | Provides ability to schedule reports that show which firewall rules are shadowed or redundant, and recommends actions to fix all reported issues. | Allows administrators to maintain an efficient firewall rule base by easily identifying ineffective and unnecessary rules |
| Firewall rule replacement guidance | Upon creation of a new rule, analyzes existing firewall rule base to recommend optimal position and application. | Significantly reduces shadowing rules. |
| Firewall policy hit count | Shows hit counts for each firewall via meters, as well as filters that display which rules are hit the least. Security Director also has the ability to keep a lifetime hit count. | Allows administrators to assess effectiveness of each firewall rule and quickly identify unused rules, resulting in a better managed firewall environment. |
| Live threat map | Displays where threats are originating in near real time and allows you to take action to stop them. | Provides near real-time insight into network-related threats. Allows you to block traffic going to or coming from a specific country with a single click. |
| Innovative application visibility and management |
|
Delivers greater visibility, enforcement, control, and protection over the network. |
| Simplified threat management | Reports where threats are originating and where they are going via a global map. Blocking a country is easy; simply mouse over the country to take action. | Provides insight needed to effectively manage networkrelated threats. Allows you to block traffic going to or coming from a specific country with a single click. |
| Snapshot support | Allows users to snapshot, compare, and roll back configuration versions. | Simplifies configuration changes and allows recovery from configuration errors. |
| Policy life cycle management | Provides ability to manage all phases of security policy life cycles, including create, deploy, monitor, remediate, and maintain. |
|
| Drag-and-drop | Allows firewall, IPS, and NAT rules to be reordered by simply dragging them to a new location. | Enables firewall, IPS, and NAT objects to be added or copied by dragging them from one cell to another, or from a pallet located at the bottom of the policy table. |
| VPN auto provisioning and import | Simply tell Security Director which VPN topology to use and which devices you want to participate in the topology, and Security Director will auto-provision the tunnels. If you have an existing Juniper VPN environment, Security Director can import the VPNs to provide an easy and effective way to manage them. | Makes pre-existing SRX Series VPNs easier to manage. |
| Role-based access for policies and objects | Allows devices, policies, and objects to be placed within domains and assigns read/write permissions to a user. | Provides customers a way to segment administrative responsibility for policies and objects. |
| REST APIs for automation | Provides RESTful APIs that can be used in conjunction with automation tools. | Automates configuration and management of physical, logical, or virtual SRX Series devices. |
| Logging and reporting through Junos Space Log Director application | Enables integrated logging and reporting. | Tight coupling with Junos Space Security Director:
Direct access to Junos Space Security Director policies and objects:
SRX Series health monitoring:
System log forwarding to security information and event management (SIEM) |
Specifications:
Client Browser Support
Security Director is best viewed on the following browsers:
- Google Chrome v.33.x and above
- Internet Explorer v.10.x and above
- Firefox v.30.x and above
- Safari v.7.x and above
VMware Version
Junos Space works with VMware vSphere 4.0 and above.
Junos (Operating System) Software
The SRX Series Services Gateways run Junos OS software. Junos Space Security Director runs on Juniper devices running Junos OS 10.3 and later releases.
Junos Space Network Management Platform
Junos Space Security Director 16.1 runs on Junos Space 16.1.
Documentation:
Download the Juniper Networks Junos Space Security Director Data Sheet (PDF).
Pricing Notes:
- All Prices are Inclusive of GST
- Pricing and product availability subject to change without notice.
Our Price: Request a Quote
Our Price: Request a Quote
Our Price: Request a Quote

